Secure your Opensource Dependencies
Secure your Opensource Dependencies
Start with a secure foundation, save time spent on triaging vulnerabilities and minimise attack surface


From a long list of unfixed vulnerabilities to a secured software supply chain

Close to Zero Vulnerabilities

<24 hrs TAT for any CVE fixed upstream

SBOMs for security compliance

Reduced size for faster deployements


From a long list of unfixed vulnerabilities to a secured software supply chain

Close to Zero Vulnerabilities

<24 hrs TAT for any CVE fixed upstream

SBOMs for security compliance

Reduced size for faster deployements


From a long list of unfixed vulnerabilities to a secured software supply chain

Smart Task Prioritization with AI Insights

<24 hrs TAT for any CVE fixed upstream

SBOMs for security compliance

Reduced size for faster deployements
Features
What PodArmor Offers You
Features
What PodArmor Offers You
Features
What PodArmor Offers You

Reduced Security Risk
Our images are constructed from rapidly patched open source software which is scanned hourly for any new CVEs. Since we build packages from source, we don’t depend on releases from distros and ensure they don’t have security vulnerabilities.

Reduced Security Risk
Our images are constructed from rapidly patched open source software which is scanned hourly for any new CVEs. Since we build packages from source, we don’t depend on releases from distros and ensure they don’t have security vulnerabilities.

Reduced Security Risk
Our images are constructed from rapidly patched open source software which is scanned hourly for any new CVEs. Since we build packages from source, we don’t depend on releases from distros and ensure they don’t have security vulnerabilities.

Achieve Compliance
Meet requirements for FedRAMP, NIST 800-53, PCI-DSS, SOC2, and CIS benchmarks easily without affecting productivity of your engineering team.

Achieve Compliance
Meet requirements for FedRAMP, NIST 800-53, PCI-DSS, SOC2, and CIS benchmarks easily without affecting productivity of your engineering team.

Achieve Compliance
Meet requirements for FedRAMP, NIST 800-53, PCI-DSS, SOC2, and CIS benchmarks easily without affecting productivity of your engineering team.

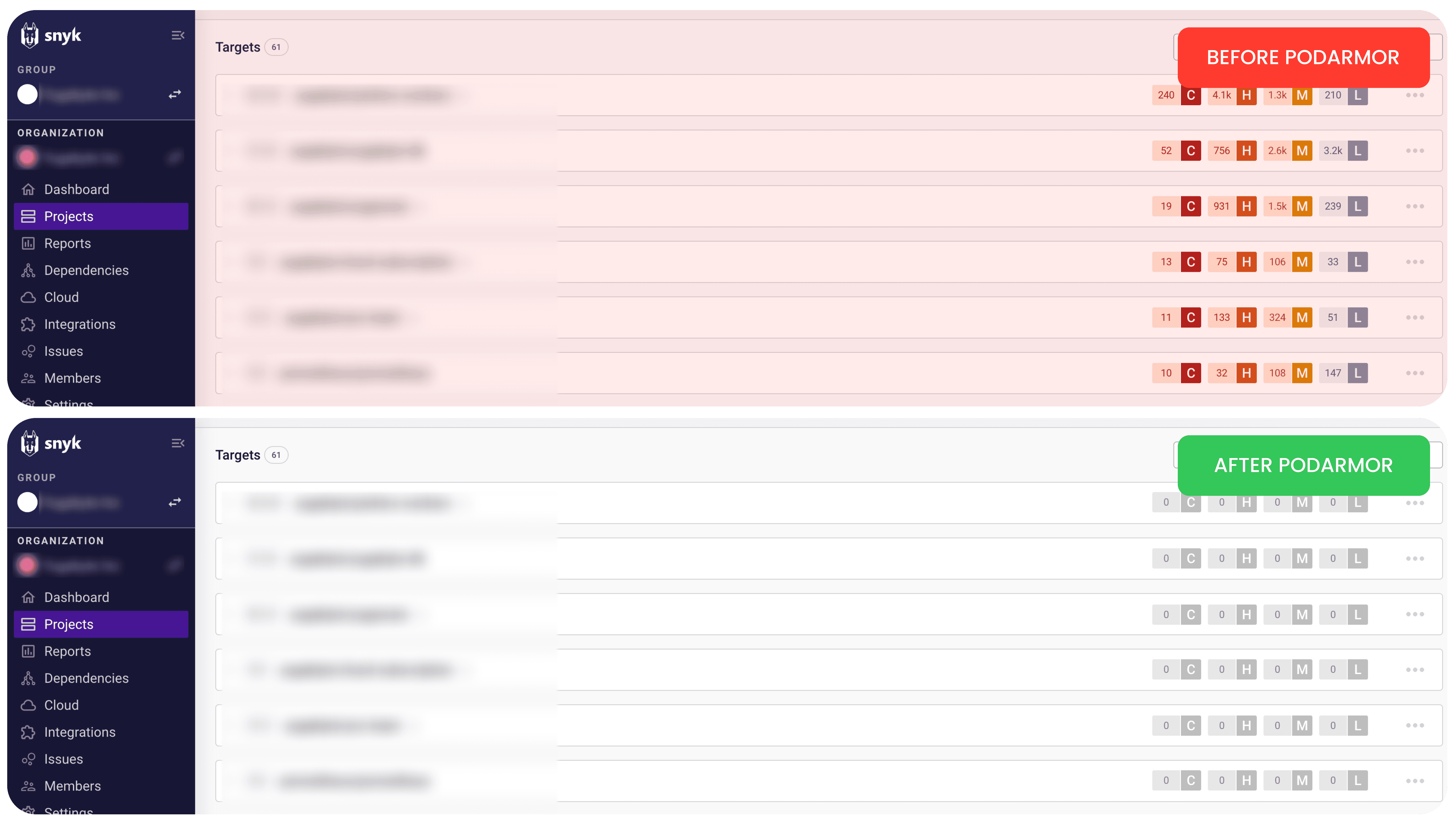
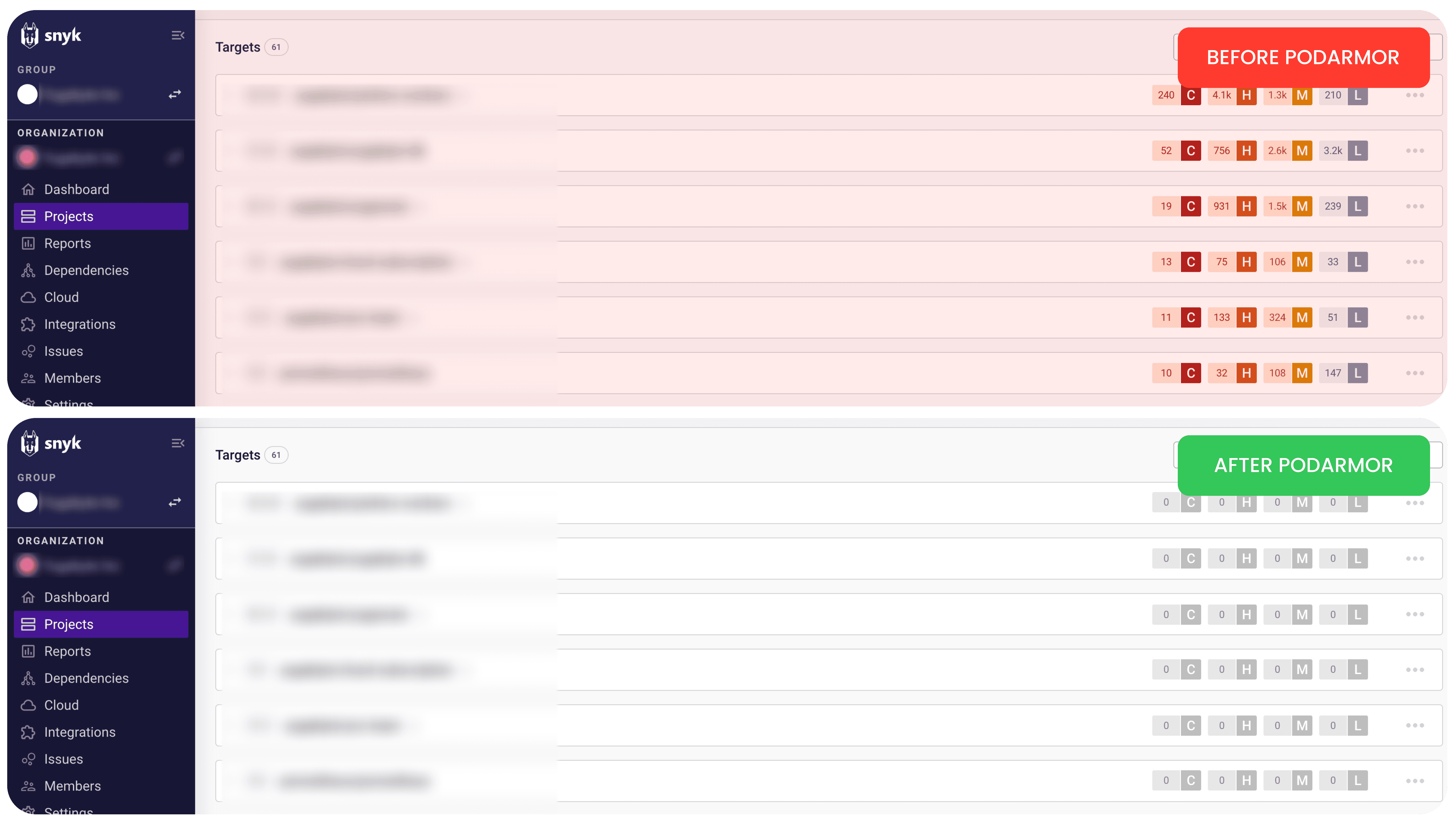
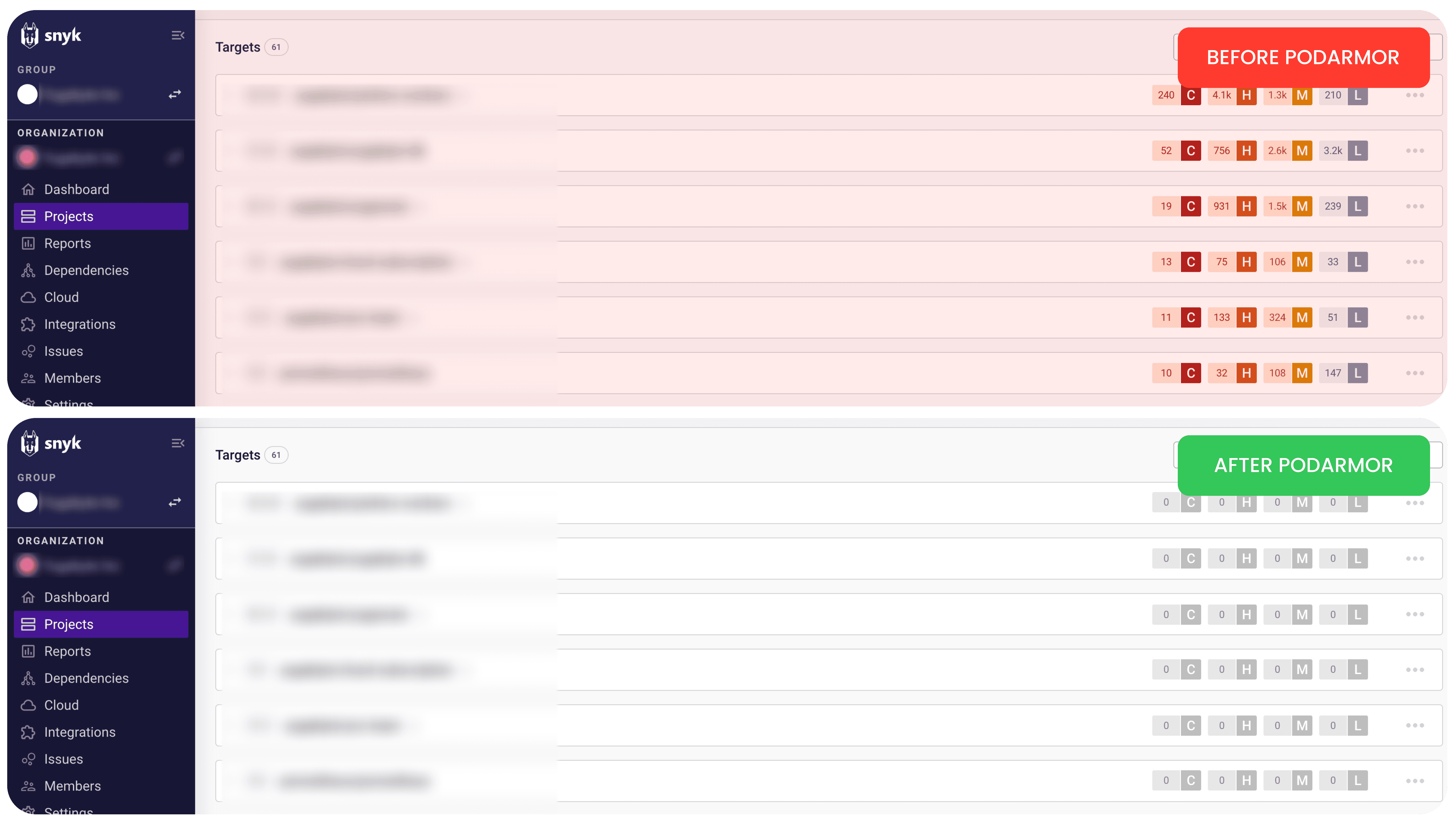
Engineering Productivity
Using our zero CVE images saves thousands of hours spent by your security engineering team in triaging and fixing CVEs detected by scanners like Synk, Trivy and Grype.

Engineering Productivity
Using our zero CVE images saves thousands of hours spent by your security engineering team in triaging and fixing CVEs detected by scanners like Synk, Trivy and Grype.

Engineering Productivity
Using our zero CVE images saves thousands of hours spent by your security engineering team in triaging and fixing CVEs detected by scanners like Synk, Trivy and Grype.
Secure Images
PodArmor in
Action
PODARMOR NODEJS IMAGE
0
CVE
49
MB
SIZE
0
DAYS
AGE
UPSTREAM NODEJS IMAGE
176
CVE
379
MB
SIZE
11
MONTH
AGE
0 CVEs
Close to zero vulnerabilities at any given time
Blazing Fast Updates
We have a maximum turnaround time of 24hrs for any CVE that has a fix already
Build time SBOMs
Comply with security guidelines requiring SBOMs for your open source dependencies
Faster Deployments
With a reduced size our images are both faster and safer to deploy
PodArmor Images
PodArmor Images
PodArmor Images
Elevate your workflow by seamlessly integrating our machine learning platform with your existing tools. We understand the importance of collaboration and compatibility, which is why our platform supports a wide array of integrations.
FAQ’s
Frequently Asked Questions
FAQ’s
Frequently Asked Questions
FAQ’s
Frequently Asked Questions
What is PodArmor?
How is PodArmor different from traditional container security solutions?
Who should use PodArmor?
How often does PodArmor update its images?
Can I migrate from existing container images to PodArmor images?
What is PodArmor?
How is PodArmor different from traditional container security solutions?
Who should use PodArmor?
How often does PodArmor update its images?
Can I migrate from existing container images to PodArmor images?
What is PodArmor?
How is PodArmor different from traditional container security solutions?
Who should use PodArmor?
How often does PodArmor update its images?
Can I migrate from existing container images to PodArmor images?

Secure your Software Supply Chain Now
Take the first step towards enhanced security—sign up now and start your journey with PodArmor.

Secure your Software Supply Chain Now
Take the first step towards enhanced security—sign up now and start your journey with PodArmor.

Secure your Software Supply Chain Now
Take the first step towards enhanced security—sign up now and start your journey with PodArmor.



















